Cloud Security for Financial Services
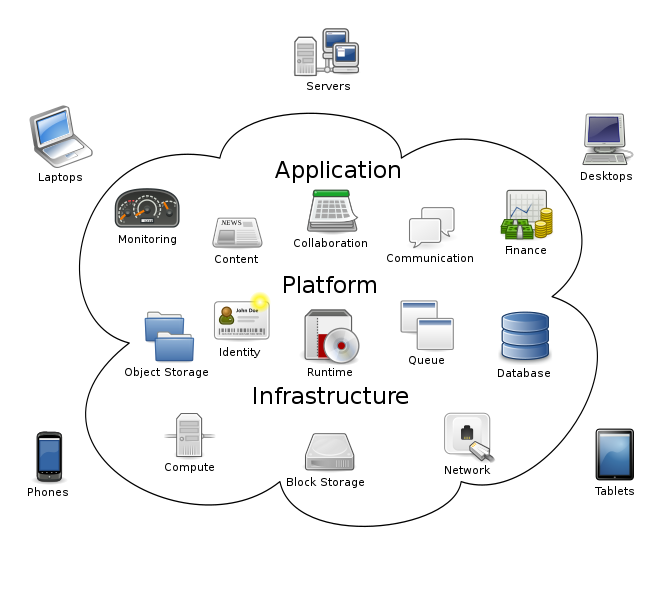
Cloud adoption is rising across industries at a steady rate, with over 90% of organizations using cloud computing technology. Now while industries have started relying on cloud services for their varied data and operational needs, there is one industry that is taking its time to adopt the idea on a holistic level i.e. Banking. With banks and financial institutions taking time to check every aspect of the cloud from the security and privacy angle, cloud computing in banking is moving at an overly cautious speed. Cloud computing is used in banks for a variety of purposes, including CRM, Data analysis, third-party solutions (like financial market data tools/calculators) etc.
While there are many benefits of using cloud technology in banking, the challenges that come with cloud adoption may be the reason so many financial institutions are lagging behind other industries. The following are some of the main issues that financial institutions face when moving to the cloud:
-
- Data privacy and security: Banks need to ensure that their data is safe and secure when it is stored in the cloud. They also need to make sure that their systems conform to any applicable regulations governing data privacy.
-
- Regulatory compliance: Banks must comply with a variety of financial industry regulations, many of which require specific procedures for handling customer data. It can be difficult for banks to meet all these requirements when their systems are hosted in the cloud.
-
- Lack of control: Financial institutions may fear that they will lose some degree of control over their systems when they move them to the cloud.
How cloud services help to keep the financial sector data safe and secure?
When cloud services are related to the bank and financial sector there are many tools and methods that can be used to secure and protect their data.
1. Firewall: The firewall is designed to provide network-based security. It provides network visibility capabilities and control for cloud-based financial services and infrastructure. The firewall maintains access control and filtering through the port-control system. Firewalls can identify and enable applications regardless of port, protocol, evasive tactics, or SSL encryption. They can also provide more control over applications, as well as deeper inspection capabilities.
2. Intrusion Detection System: It’s a system that provides the feature to monitor the network traffic for suspicious activity and issue alter that scans a network or a system for the harmful activity or policy breaching.
3. VPN (Virtual Private Networks) System: that allows you to access the internet through a virtual server with a different IP to the IP of your device. While your device is accessing a remote server just like some private network devices do through a jump box, you are not necessarily going through a single point of use. Based on the VPN, browsing activity is masked from your internet service provider. This is accomplished mainly by switching your IP address, which you should understand to get the true value of a VPN.
4. Jump Server: A jump server is a virtual machine that helps secure one’s private network by forcing traffic to sensitive devices to go through a single secure point. If you are a company that allows customers access to an online service hosted on your private network, you have a potential data security risk.
5. Backup Facility: it is a service in which the data and applications on a server are backed up and stored on a remote server. back up to the cloud to keep files and data readily available in the event of a system failure, outage, or natural disaster. Cloud backup operates by copying and storing your servers files to a server in a different physical location.
6. OAuth Authentication: it is a piece of data that represents the authorization to access resources on behalf of the end-user. It does not define a specific format for Access Tokens. This enables token issuers to include data in the token itself. Also, for security reasons, Access Tokens may have an expiration date.
7. Data Encryption: Cloud encryption is needed because its main aim is to secure and protect confidential information as it is transmitted through the Internet and other computer systems. Cloud encryption is the process of encoding or transforming data before its transfer to cloud storage. Encryption uses mathematical algorithms to transform data, may it be a text, file, or code to an unreadable form that can conceal it from unauthorized and malicious users. It is the simplest and most vital way to make sure that cloud data cannot be breached, stolen, and read by someone with an anomalous motive.
8. Data Masking: Data masking is a method of creating a structurally similar but inauthentic version of an organization’s data that can be used for purposes such as software testing and user training. The purpose is to protect the actual data while having a functional substitute for occasions when real data is not required. In data masking, the format of data remains the same only the values are changed. The data may be altered in a number of ways, including encryption, character shuffling, and character or word substitution.
Follow